Types of VPNs and How to Choose the Right One
Sending sensitive data across the internet without protection is like mailing your house keys on a postcard. That uncomfortable feeling is exactly why understanding the…

Table of Contents
Protect your online privacy and security
Fast, private, and easy to use, get Hidzo on your device and browse freely with one tap.
Get HidzoVPN
Sending sensitive data across the internet without protection is like mailing your house keys on a postcard. That uncomfortable feeling is exactly why understanding the different types of VPNs matters more than ever. From simple personal connections to complex enterprise networks, choosing the right VPN is a critical decision for managing and taking the most out of your resources.
Rather than treating all VPNs as identical digital shields, this guide breaks down the main types of VPNs, their underlying protocols, real-world strengths, hidden weaknesses, and the practical factors that should guide your choice.
A Glance at VPN Fundamentals
A Virtual Private Network (VPN) establishes a protected communication channel by creating an encrypted tunnel that carries your data across public or untrusted networks. At a fundamental level, it combines tunneling (encapsulating packets inside new ones), strong encryption for confidentiality, and authentication mechanisms to verify the identity of both endpoints.
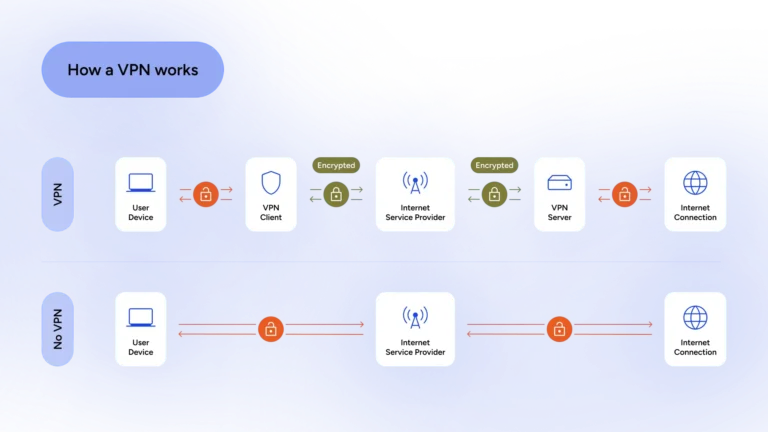
Two important distinctions are client-based versus clientless (SSL/TLS) VPNs. Client-based VPNs require dedicated software on the user’s device to create a comprehensive virtual network interface, enabling broad access and advanced routing features. In contrast, clientless VPNs leverage standard web browsers for secure access, reducing deployment friction but often limiting functionality to specific applications or web resources.
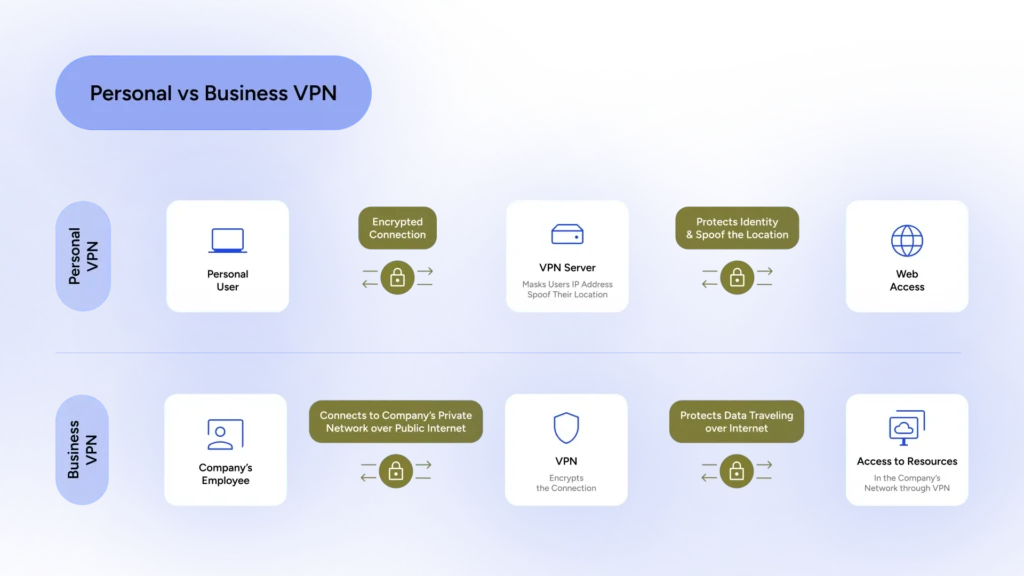
We can also classify VPNs by use case into two main categories: personal and enterprise. Personal VPNs are popular apps, like HidzoVPN, that we use to protect our online privacy and resolve geo-blocking problems. On one end is the user’s device, and on the other is unrestricted internet access. Enterprise VPNs, on the other hand, are used to share a company’s resources and files with remote workers or other branches.
Primary Types of VPNs
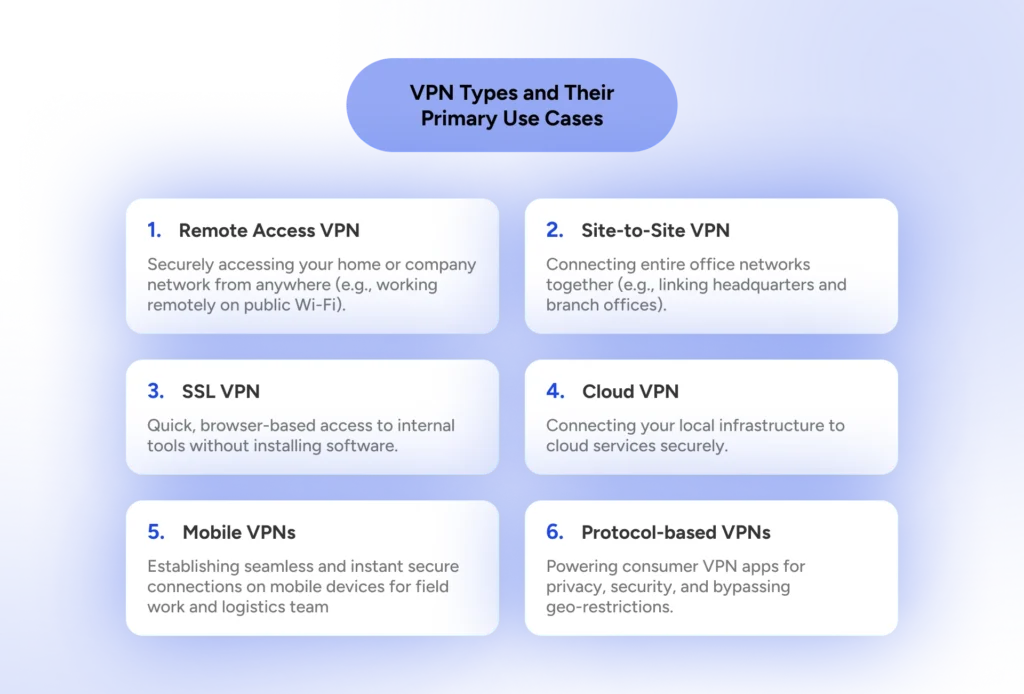
The world of VPNs is best understood by examining their primary architectural designs. These architectures determine how connections are established, who can access what, and how well the solution scales. While many VPNs share similar underlying protocols, their deployment models create distinct strengths and limitations. Let’s explore the core types with clarity and a touch of perspective.
1. Remote Access VPNs (Client-to-Site)
Remote access VPNs allow individual users, such as remote employees, traveling professionals, or work-from-home teams, to securely connect to a central private network from anywhere. A software client installed on the user’s device creates an encrypted tunnel to the organization’s VPN gateway, granting access to internal resources as if the user were physically in the office.
These VPNs offer excellent flexibility but come with management overhead, including endpoint-security dependencies and the need to scale user authentication. Think of it as giving each employee their own secure key to the office building: it’s convenient, but you still need to ensure every keyholder behaves responsibly.
2. Site-to-Site VPNs
Site-to-site VPNs, also known as gateway-to-gateway VPNs, connect entire networks to one another over the internet. They are commonly used to link branch offices to headquarters (intranet VPNs) or to securely connect with partner organizations (extranet VPNs). Once established, users on either network can access resources transparently without installing client software on individual devices.
These setups excel in seamless resource sharing and centralized management but introduce complexity in routing, firewall rules, and high-availability configurations. A single misconfigured tunnel can disrupt connectivity across locations.
3. SSL/TLS VPNs (Clientless)
SSL/TLS VPNs provide secure access without requiring dedicated client software. Users connect through a standard web browser, making them particularly convenient for contractors, partners, or scenarios where installing software is restricted.
They excel at granular, application-level access control rather than granting full network access. However, this convenience often comes at the cost of limited support for non-web applications and potentially higher latency for complex workflows.
4. Cloud VPNs and VPN as a Service (VPNaaS)
Cloud VPNs integrate directly with major cloud platforms, enabling secure connectivity between on-premises infrastructure and cloud environments, or between different cloud providers in multi-cloud setups. They offer dynamic scaling, simplified management through cloud consoles, and native integration with virtual private clouds (VPCs). While they reduce the burden of maintaining physical appliances, they require careful attention to identity and access management, as well as proper routing configurations to avoid exposing resources unintentionally.
5. Mobile VPNs
No, we don’t mean that VPN app you use to unblock your internet access. By mobile VPNs, we mean services that address the unique challenges of roaming devices that frequently switch between Wi-Fi, cellular, and other networks. They emphasize persistent connectivity, fast reconnection after signal drops, and resilience to network changes. These are particularly valuable for field teams, delivery personnel, or anyone whose work depends on uninterrupted, secure access while on the move.
6. Personal / Consumer VPNs (Protocol-Based)
Personal VPNs are designed for individual users seeking privacy, secure public Wi-Fi usage, or bypassing geo-restrictions. Unlike enterprise remote-access solutions, they typically route traffic through a provider’s global server network rather than a corporate gateway. They prioritize ease of use and broad device support (especially smartphones), though they generally offer less granular control (for example, user access levels) and weaker policy enforcement than business-oriented deployments.
HidzoVPN is an excellent example of a personal VPN because it delivers the privacy protection that people need in today’s wired world, and using it is as easy as tapping Connect. Since it’s a privacy solution for everyone, it offers both a freemium and a Premium version, and even HidzoVPN Premium offers extremely competitive pricing.
Specialized and Emerging VPN Types
Beyond the primary architectures, several specialized and emerging VPN types have evolved to address modern challenges such as zero-trust security models and increasingly sophisticated threat landscapes. These solutions often go beyond traditional tunneling to deliver more granular control, better scalability, or enhanced privacy features.
Double-Hop (and Multi-Hop) VPNs
Double-hop VPNs route your traffic through two (or more) VPN servers in sequence before reaching its final destination. This cascaded encryption adds an extra layer of privacy by ensuring that no single server knows both your origin and your destination.
While attractive for users with high privacy requirements, the added hops naturally increase latency and reduce overall speed. Consider it the digital equivalent of taking two separate taxis with different drivers: it’s much harder for anyone to follow your complete journey, but definitely slower than taking one direct ride.
Hardware vs. Software VPN Solutions
Hardware VPNs utilize dedicated appliances or routers for high-performance, always-on connections, offering excellent throughput and security isolation. Software and virtual VPN solutions, including containerized deployments, provide greater flexibility and easier scaling in virtualized or cloud-native environments. The choice often depends on performance demands, budget constraints, and operational preferences.
Advanced and Integrated Models
Modern enterprise environments are increasingly adopting integrated frameworks such as Secure Access Service Edge (SASE) and Zero-Trust Network Access (ZTNA). These approaches combine VPN-like connectivity with advanced security services, including continuous verification, least-privilege access, and threat prevention delivered from the cloud. Additionally, service providers commonly use technologies like MPLS VPNs and Virtual Private LAN Service (VPLS) for large-scale, high-reliability deployments.
Looking ahead, emerging considerations include quantum-resistant cryptography to future-proof VPNs against potential quantum-computing threats. These specialized types reflect the ongoing evolution of VPN technology from simple encrypted tunnels toward more intelligent, context-aware security solutions.
Comparing VPN Types and Use Cases
Selecting the right VPN type and protocol requires more than comparing individual features. It demands a structured evaluation based on your specific operational context, security requirements, and performance expectations. Different combinations of VPN architectures and protocols excel under different conditions. The goal is to avoid a one-size-fits-all approach and instead align the solution with your actual needs.
Here is a comparison across the primary VPN architectural types:
| VPN Type | Ease of Deployment | Performance Impact | Best Use Cases | Key Limitations |
|---|---|---|---|---|
| Remote Access | Medium | Moderate | Remote workers, mobile teams | Endpoint security dependency, user management overhead |
| Site-to-Site | Medium-High | Low to Moderate | Connecting offices or partners | Complex routing, single point of failure risk |
| Personal / Consumer | Very Easy | Low to Moderate | Privacy, public Wi-Fi, geo-unblocking | Limited policy control, shared infrastructure |
| Cloud VPN / VPNaaS | Easy | Low | Cloud-to-on-prem or multi-cloud | Potential vendor lock-in, cloud cost management |
| SSL/TLS (Clientless) | Very Easy | Moderate | Contractors, web-based access | Limited to specific applications |
| Double/Multi-Hop | Medium | High (negative) | High-privacy or sensitive operations | Significant speed reduction |
How to Choose the Right VPN Type
Follow this structured approach to make an informed decision:
- Define Your Primary Objectives
Start by answering: Is your priority confidentiality, regulatory compliance, performance, ease of use, or scalability? For example, a financial institution may emphasize auditability and zero-trust principles, while a software development team might prioritize speed and developer experience.
- Assess Your Environment and Constraints
Consider network conditions (firewall restrictions, censorship), device types (mobile vs. desktop), user count, and integration requirements with existing systems such as SD-WAN, identity providers, or cloud platforms.
- Evaluate Your Threat Model
Are you protecting against casual eavesdroppers on public Wi-Fi, sophisticated nation-state actors, or insider threats? High-sensitivity environments may benefit from multi-hop configurations or quantum-resistant options, while standard corporate remote access can often rely on well-implemented WireGuard or IKEv2.
- Balance Trade-offs
- Need maximum speed and simplicity? → Lean toward WireGuard with a Remote Access or Cloud VPN architecture.
- Require strong firewall traversal and flexibility? → Choose OpenVPN.
- Need seamless mobility for field teams? → IKEv2/IPsec paired with Remote Access or Mobile VPN.
- Connecting multiple fixed locations? → Site-to-Site VPN with IKEv2 or WireGuard.
- High privacy demands with acceptable speed loss? → Consider Double-Hop setups.
- Consider Operational Factors
Factor in long-term maintenance, certificate/key management, monitoring capabilities, compliance requirements (such as GDPR or industry standards), and future growth. Always plan for proper logging policies and leak protection (DNS, WebRTC, IPv6).
Common Pitfalls to Avoid
- Assuming “more encryption layers = better security” without considering performance degradation.
- Neglecting endpoint security: a VPN is only as secure as the devices connecting through it.
- Overlooking ongoing certificate renewal and software updates, which can create hidden vulnerabilities.
- Choosing a solution based solely on ease of setup rather than long-term scalability.
By systematically evaluating your needs against these criteria, you can move from guesswork to a confident, technically sound decision. The “best” VPN is not the most popular one; it is the one that fits your unique technical and security context.
VPN Protocol: The Beating Heart of Every VPN
The true character of any VPN lies in its tunneling protocol, which involves the rules that govern how data is encapsulated, encrypted, authenticated, and transported. Choosing the right protocol often has a greater impact on security, speed, and reliability than the architectural type itself. Understanding these differences empowers you to match the protocol to your specific threat model, performance requirements, and operational environment. Here are the major protocols worth knowing:
OpenVPN
OpenVPN remains one of the most versatile and trusted protocols. It is open-source, highly configurable, and supports both UDP and TCP. It offers strong AES-256-GCM encryption and excellent firewall traversal. Its flexibility makes it suitable for many enterprise and privacy-focused deployments, though it carries slightly higher overhead.
WireGuard
WireGuard brings modern simplicity with a tiny codebase, exceptional speed, low latency, and efficient resource usage. It uses state-of-the-art cryptography (ChaCha20-Poly1305 and Curve25519) and reconnects almost instantly. Its minimal design reduces the attack surface, making it increasingly popular for performance-sensitive environments.
IPsec with IKEv2
IKEv2/IPsec is a robust enterprise-grade protocol known for excellent mobility and seamless reconnection when switching networks. It provides strong security and native support on most platforms, though it requires more careful configuration of certificates and policies.
Legacy Protocols
Older options such as L2TP/IPsec, SSTP, and PPTP still exist but are generally less recommended today. PPTP, in particular, is considered cryptographically weak and should be avoided in production environments.
Here is a short comparison of VPN protocols:
| Protocol | Speed | Security Level | Configuration Complexity | Best For | Notable Weakness | Open Source |
|---|---|---|---|---|---|---|
| WireGuard | Excellent | Very High | Very Low | Performance, modern deployments | UDP-only (can be blocked) | Yes |
| OpenVPN | Good | Very High | Medium | Flexibility, restrictive networks | Higher overhead | Yes |
| IKEv2/IPsec | Very Good | High | Medium-High | Enterprise, mobile users | Complex certificate management | No |
| L2TP/IPsec | Moderate | Moderate | Medium | Legacy compatibility | Slower, larger overhead | No |
| SSTP | Good | High | Medium | Windows-heavy environments | Microsoft proprietary | No |
| PPTP | Fast | Very Low | Low | Obsolete testing only | Cryptographically broken | No |
Key Takeaways:
- WireGuard currently leads in speed and simplicity, making it ideal for most everyday and performance-oriented use cases.
- OpenVPN remains the most flexible and censorship-resistant choice when maximum compatibility is needed.
- IKEv2 shines in enterprise mobility scenarios where seamless roaming is critical.
- Legacy protocols should generally be avoided for new deployments due to security or efficiency limitations.
On a related note:
The 2026 Guide to Best VPN Protocols for Every Scenario
Implementation Considerations and Best Practices
Now that you understand the different types of VPNs and protocols, it’s time to talk about turning theory into reality. A well-designed VPN can work beautifully on paper but become a source of frustration if implementation details are overlooked. Here are the key considerations and best practices that separate smooth deployments from painful ones.
Deployment Architectures and Integration
When rolling out a VPN, think beyond just the tunnel. Consider how it integrates with your existing infrastructure. For enterprise setups, placing the VPN gateway behind a next-generation firewall or using it as part of a SASE framework often provides better security layering. In cloud environments, leverage native VPNaaS options and ensure proper routing with VPC peering or transit gateways to avoid accidental exposure of resources.
Certificate and Key Management
Proper cryptographic hygiene is non-negotiable. Use strong certificate authorities (CAs), implement automated certificate rotation, and prefer short-lived certificates where possible. Poor key management is one of the most common ways VPNs get compromised. Treat your private keys like your house keys: if you lose them or leave them lying around, someone else might happily walk in.
Monitoring, Logging, and Troubleshooting
Implement comprehensive monitoring of VPN connections, including connection attempts, bandwidth usage, and error rates. Centralized logging helps detect anomalies such as unusual login patterns or potential tunnel leaks. Common troubleshooting issues include DNS leaks, IPv6 leakage, and split-tunneling misconfigurations. Tools that provide real-time visibility into tunnel health and latency can save hours of headache. Always test thoroughly after any configuration change, because nothing ruins a Monday quite like discovering half your remote team can’t connect.
Security Hygiene and Best Practices
- Enforce multi-factor authentication (MFA) for all VPN logins.
- Combine VPN usage with strong endpoint protection and device posture checks.
- Disable unnecessary legacy protocols and keep software/firmware regularly updated.
- Carefully configure split tunneling policies to balance usability with security risks.
- For high-security environments, consider disabling client-side split tunneling entirely and routing all traffic through the VPN.
- Regularly audit access rights and remove stale user accounts promptly.
Future-Proofing Your VPN
Plan for evolving threats by evaluating support for post-quantum cryptography and zero-trust principles. As networks grow more dynamic, solutions that integrate seamlessly with continuous authentication and micro-segmentation will offer better long-term protection.
A successful VPN implementation is less about flashy features and more about thoughtful design, disciplined execution, and ongoing maintenance. Get these fundamentals right, and your VPN will quietly do its job: protecting data without drawing attention to itself.
Conclusion
The key takeaway is that there is no universal “best” VPN. The right choice always depends on your specific needs, threat model, performance expectations, and operational reality.
By understanding the strengths and limitations of Remote Access, Site-to-Site, Cloud VPNs, SSL/TLS, and emerging models, along with the protocols that power them, you’re now far better equipped to make informed, confident decisions instead of relying on marketing hype or default recommendations.
Choose thoughtfully, implement carefully, and don’t forget to revisit your setup as your needs and the threat landscape evolve.
FAQs
There are six primary architectural types, including Remote Access, Site-to-Site, SSL/TLS, Cloud, Mobile, and Personal VPNs.
The most common and trusted protocols used today are OpenVPN, WireGuard, and IKEv2/IPsec.
An intranet VPN securely links an organization’s own branch offices to its headquarters. An extranet VPN is used to create a secure connection between an organization and its external partners or stakeholders.
An IPsec VPN is a robust, enterprise-grade solution often paired with the IKEv2 protocol to provide strong security and seamless reconnection. It is highly valued for its stability on mobile devices when switching between different networks.
WireGuard is a modern, high-speed protocol known for its simple codebase and state-of-the-art cryptography. It offers exceptional performance and low latency, making it the current leader for everyday and speed-sensitive use cases.
An MPLS (Multiprotocol Label Switching) VPN is a technology used by service providers for large-scale, high-reliability network deployments.
Always-on VPNs utilize hardware appliances or specific software configurations to maintain a constant, high-performance connection. They are designed to ensure that a device is protected the moment it connects to the internet without requiring manual user intervention.
A mobile VPN is designed specifically for users who frequently roam between Wi-Fi and cellular networks, ensuring the connection doesn’t drop during the switch.




